Deploy and Configure SonarQube
In this post, I will walk you through some of the best practices that helps you to complete post deployment configuration of SonarQube.
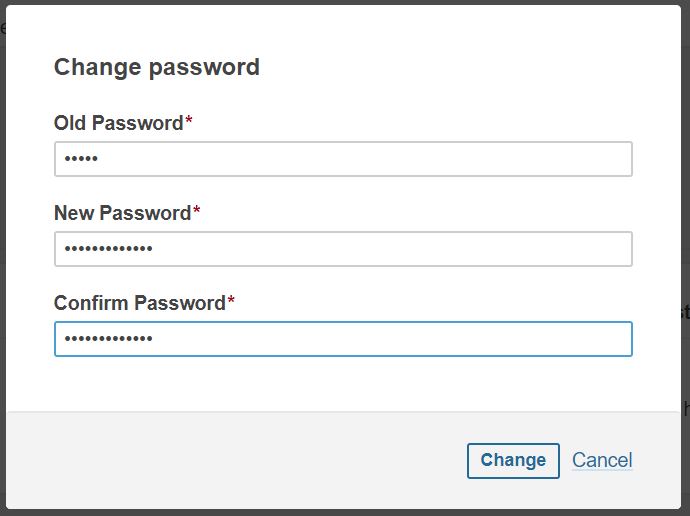
Change Admin Password
First Thing First
Post-deployment login into SonarQube using following default credentials for SonarQube.
- user: admin
- password: admin
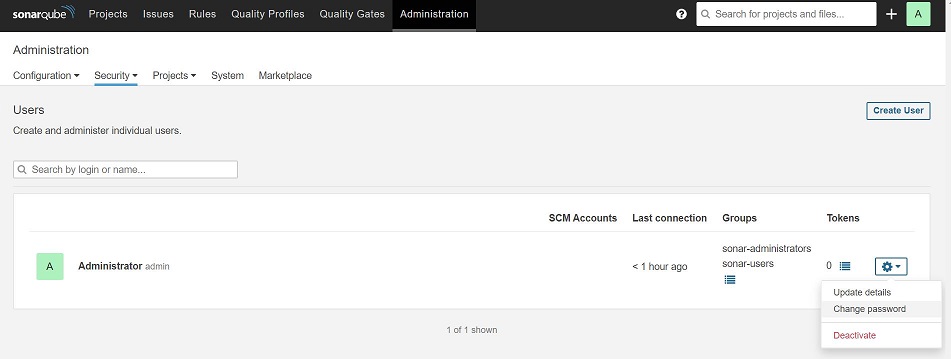
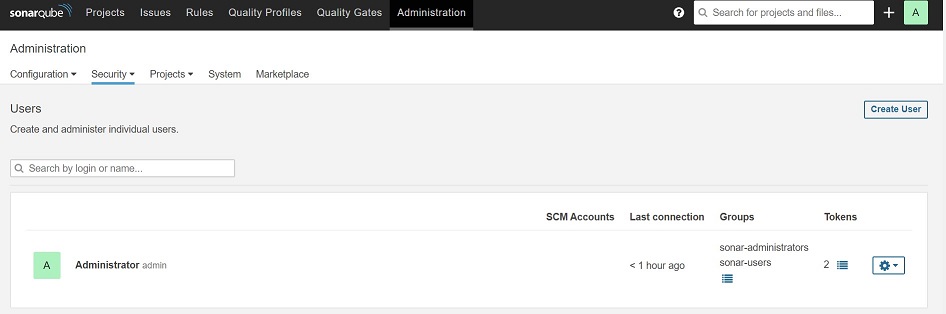
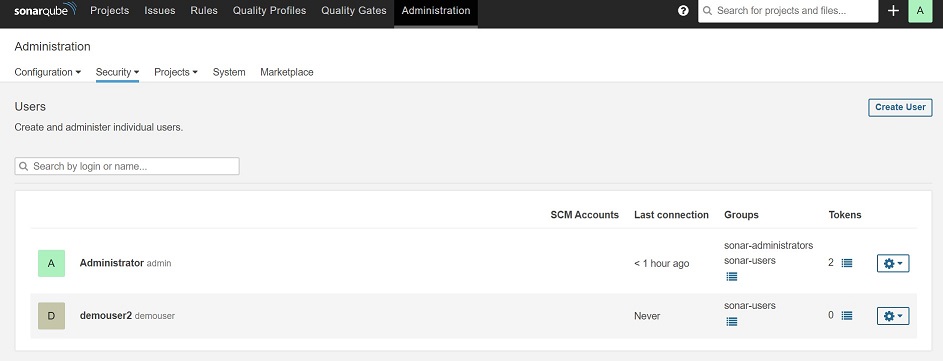
After login, go to the administration and select security - users
Change Password
Force authentication
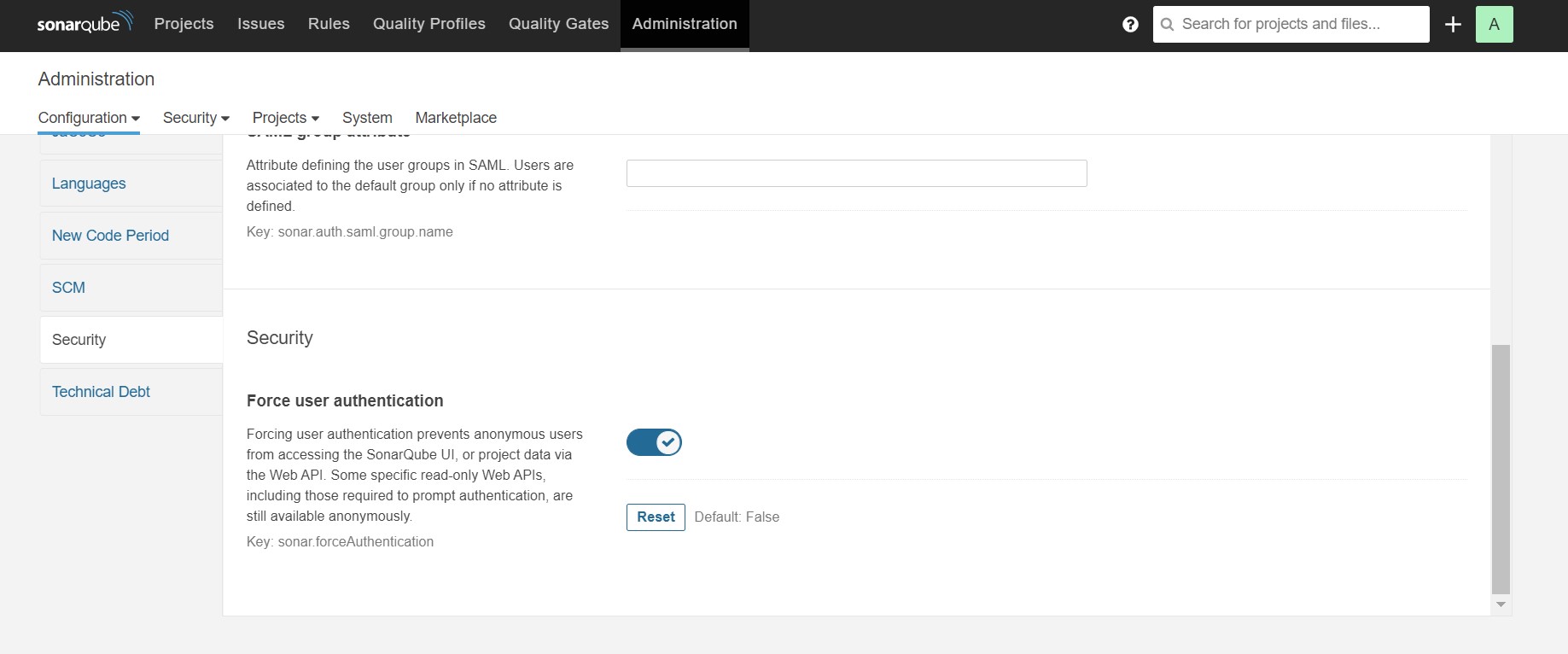
After enabling the force security option no one able to see the project’s analysis summary without login.
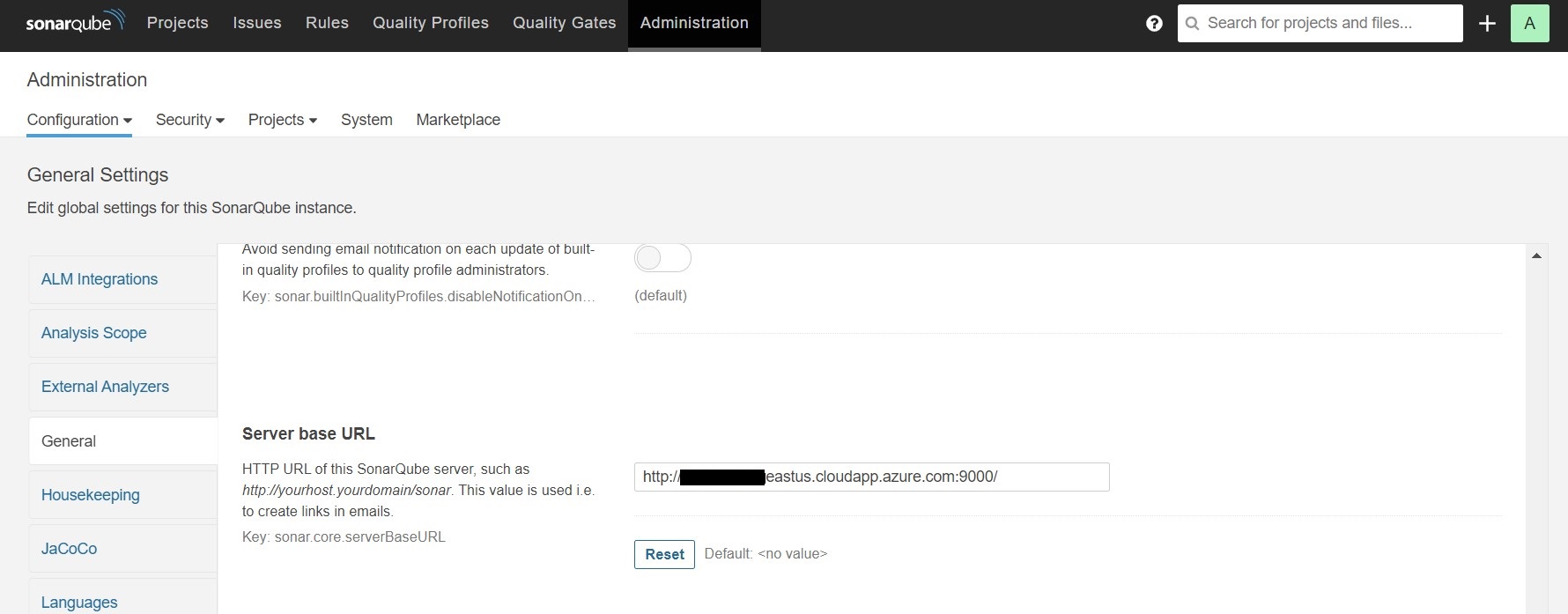
Configure Server base URL
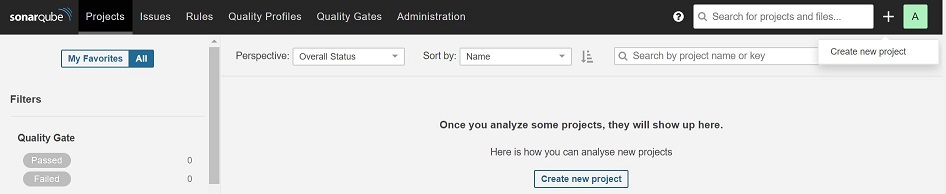
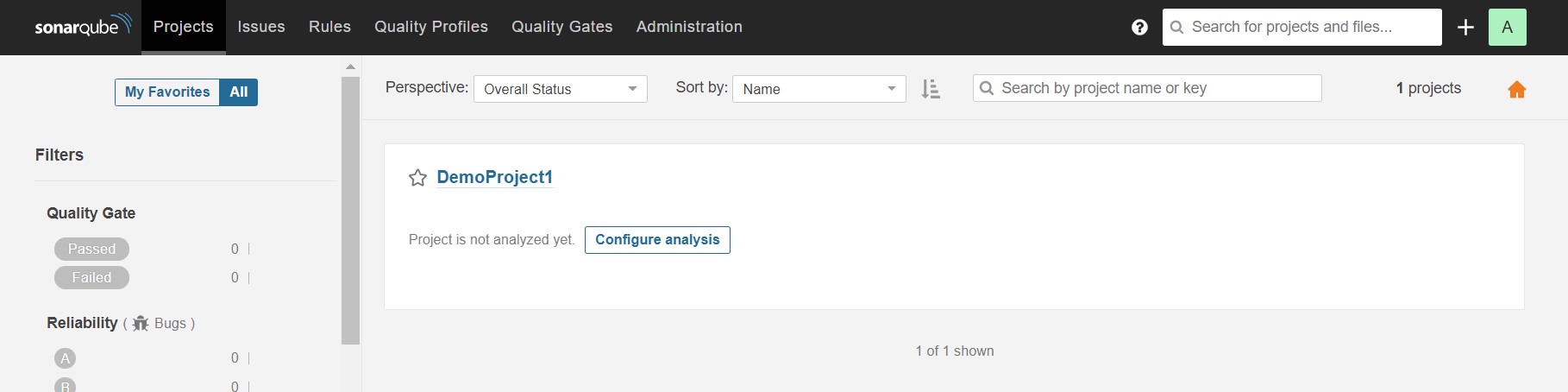
Create Project
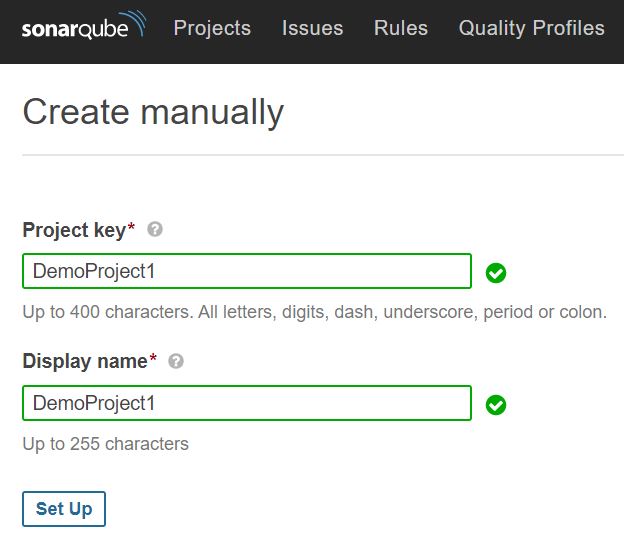
SonarQube provides 2 ways to create a project.
Provide Project Key (without space) and Display Name.
This key will require when you will configure the Sonarqube with Azure Pipelines.
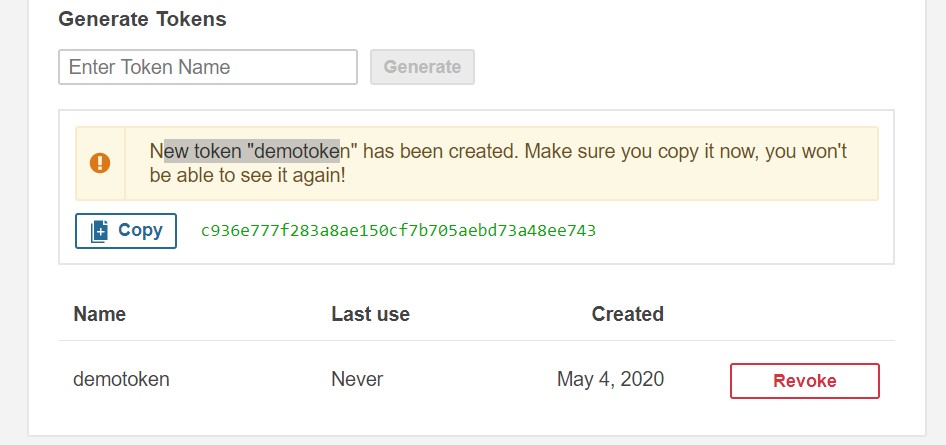
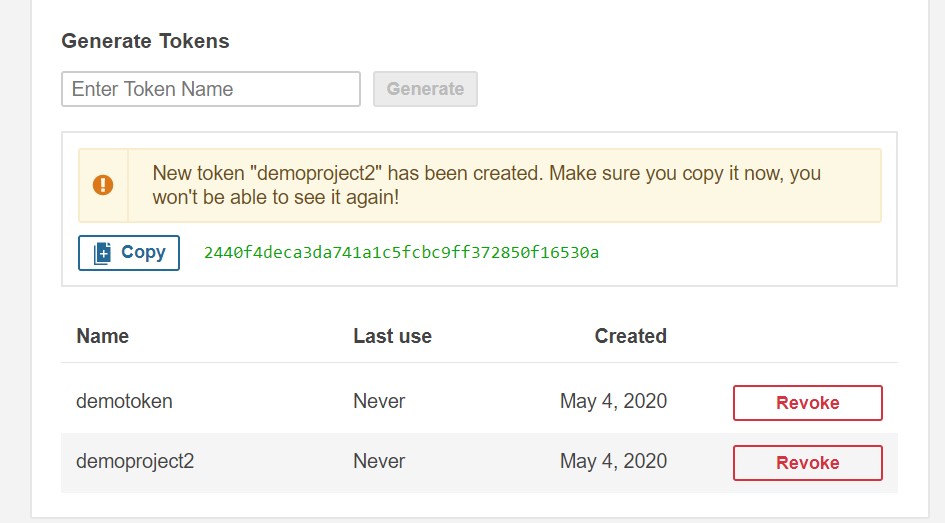
Configure Tokens
Recommanded
If you want to enforce security by not providing credentials of a real SonarQube user to run your code scan or to invoke web services, you can provide a User Token as a replacement of the user login. This will increase the security of your installation by not letting your analysis user’s password going through your network.
These tokens are used to create Service endpoint with Azure DevOps.
Administrator - My Account - Security
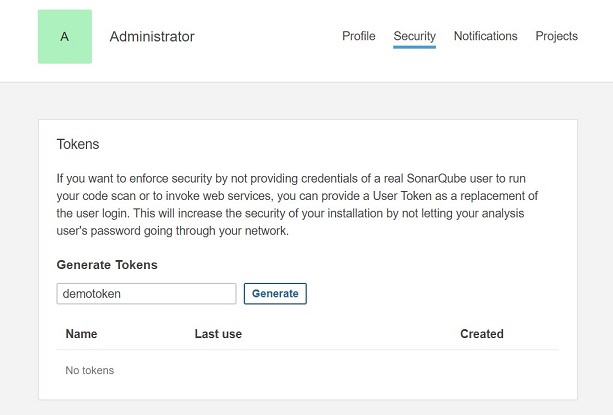
You can have 1 token across the projects or you can have individual tokens.
Create and Add Users
Create User
SonarQube allows creating local users
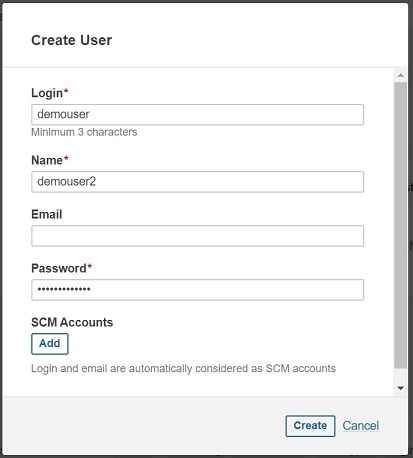
Add User to project
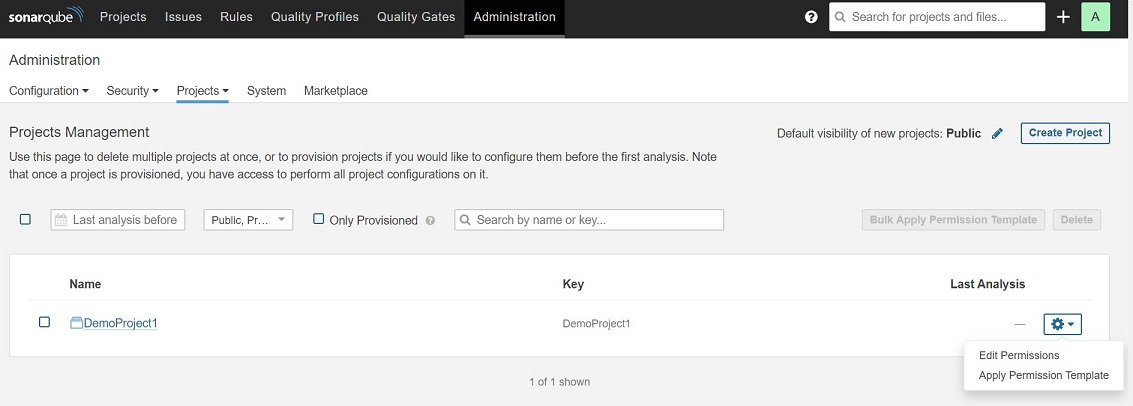
Add user to project with desired permissions by selecting the checkbox.
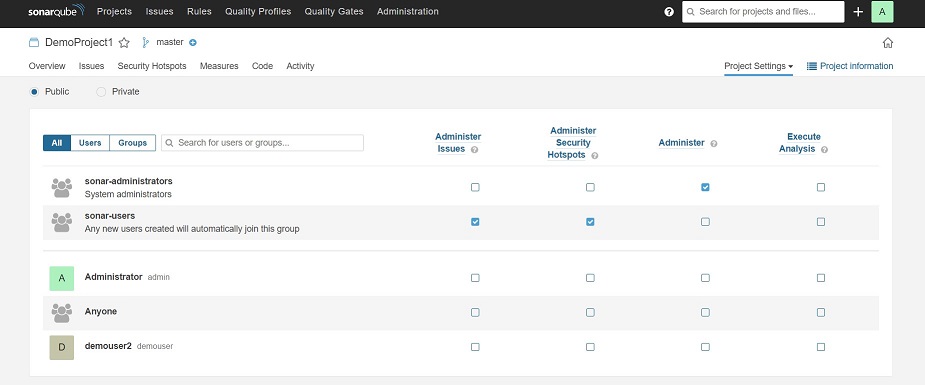
Let’s assign this user Execute Analysis Permission and see the difference.
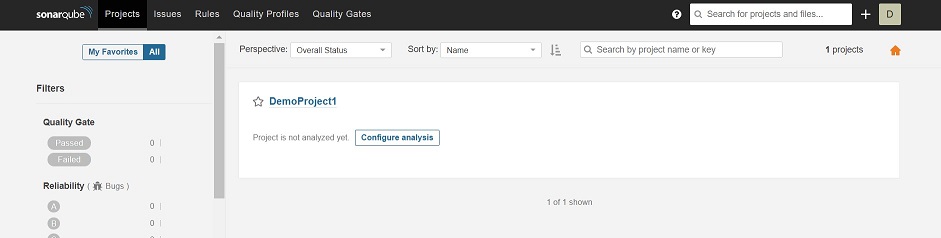
Menu options are limited now.
Configure with AAD
Refer sonar-auth-aad document to configure AAD authentication for SonarQube.
Work with Azure DevOps Pipeline
Refer MS Documentation to configure SonarQube server with Azure DevOps pipeline.
Other Readings
- SonarQube Tool Assessment- 1 (understand reporting)
- SonarQube Tool Assessment- 2 (understand plan and pricing)
Related Posts
- Deploy SonarQube as Azure Web App Container
- People, Process, Product - DevOps - SonarQube Tool Assessment- 2
- People, Process, Product - DevOps - SonarQube Tool Assessment- 1
About Ajeet Chouksey